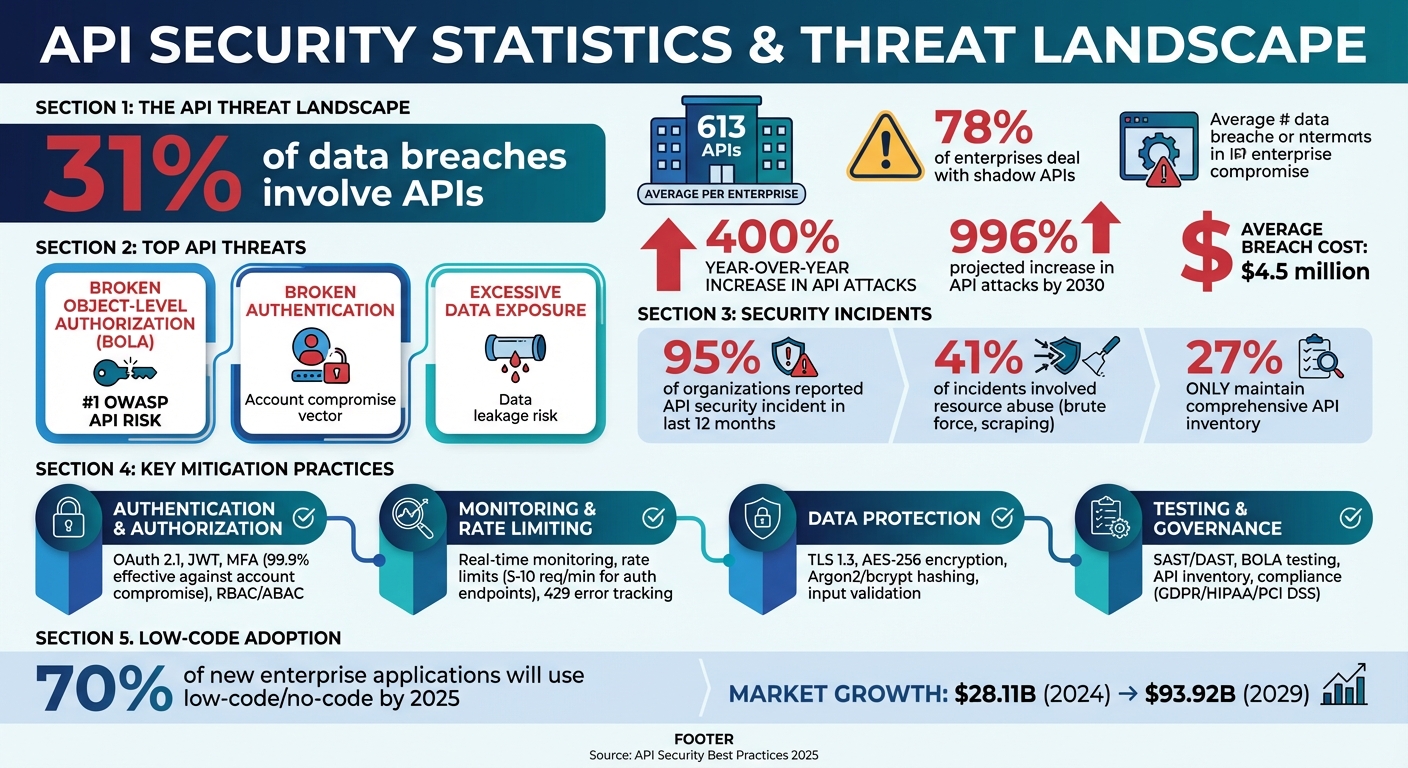
APIs power modern software but are increasingly targeted by cyberattacks, contributing to 31% of data breaches. With 613 APIs on average per enterprise and 78% dealing with shadow APIs, securing APIs is a top priority. Key threats include Broken Object-Level Authorization (BOLA), Broken Authentication, and Excessive Data Exposure.
To mitigate risks:
- Authentication & Authorization: Use OAuth 2.1, JWTs, and MFA. Employ Role-Based Access Control (RBAC) or Attribute-Based Access Control (ABAC) for precise permissions.
- Monitoring & Rate Limiting: Implement tools to track traffic and enforce limits to prevent abuse.
- Data Protection: Use TLS 1.3 for encryption, validate inputs, and hash sensitive data.
- Testing & Governance: Regularly test for vulnerabilities like BOLA and maintain an updated API inventory to avoid shadow APIs.
Low-code/no-code platforms simplify API security by offering built-in tools like MFA, JWT validation, and encryption. By following these practices, businesses can reduce the risk of breaches and protect critical systems effectively.
API Security Threats and Best Practices Statistics 2024-2025
API Security Workshop | Protect Your APIs with Best Practices
sbb-itb-3a330bb
Authentication and Authorization Best Practices
Authentication confirms who the requestor is, while authorization determines what actions they are allowed to perform. Both are essential for protecting sensitive data and functionality. Weaknesses in these areas can leave APIs vulnerable to attacks, making them a critical layer of defense.
Authentication Methods
OAuth 2.0 is widely used for granting limited access across applications. It allows users to share specific data with third-party apps without exposing their passwords. By issuing short-lived access tokens, it minimizes risk if a token is compromised. The updated OAuth 2.1 standard now mandates Proof Key for Code Exchange (PKCE) for all clients, including server-side ones, to guard against authorization code interception.
JSON Web Tokens (JWT) are a popular choice for stateless authentication. They package user claims and a cryptographic signature into a compact token, enabling servers to verify their authenticity without needing a database lookup. This makes JWTs especially suited for microservices and single-page applications. However, it’s crucial to validate the signature, expiration (exp), issuer (iss), and audience (aud) with every request. Always allowlist accepted algorithms like RS256 and block tokens using the none algorithm to prevent signature bypass attacks.
For high-security use cases - like financial APIs or webhooks - HMAC Request Signing is a strong option. Pairing it with mutual TLS (mTLS) for service-to-service communication can help prevent tampering and replay attacks, particularly in zero-trust environments.
Multi-Factor Authentication (MFA) is a must for user-facing APIs. Microsoft’s research shows that MFA can thwart 99.9% of account compromise attempts. Beyond login, apply MFA to sensitive actions like password resets or privilege upgrades. Time-based one-time passwords (TOTP) are generally safer than SMS codes, which are vulnerable to SIM-swapping attacks. For maximum security, consider passkeys (FIDO2) for phishing-resistant authentication. Always enforce HTTPS - credentials and tokens should never travel over unencrypted HTTP. Use HttpOnly cookies with Secure and SameSite attributes to guard against cross-site scripting (XSS). Once authentication is solid, granular authorization can further lock down API interactions.
Authorization Frameworks
Strong authentication needs to be paired with precise authorization to maintain API security. Role-Based Access Control (RBAC) is a straightforward approach that assigns permissions to roles instead of individual users. It’s easy to implement and audit, making it a go-to for business applications with predictable permission structures. However, RBAC alone may not prevent Broken Object-Level Authorization (BOLA). Even if a user’s role is correct, you still need to verify their access to specific resources on every request.
Attribute-Based Access Control (ABAC) goes a step further by enabling fine-grained, context-aware decisions. It takes into account user attributes, resource properties, and environmental factors like time or location. Though more complex to set up, ABAC works well in industries like healthcare and finance, where access often depends on multiple conditions. For instance, a doctor might only view patient records during their shift and for patients assigned to their care.
A zero-trust security model assumes no request is inherently safe. Every request must be authenticated and authorized, regardless of where it originates. This approach pairs effectively with mTLS for internal microservices, ensuring that each service verifies the identity of its caller. To prevent brute-force and credential stuffing attacks, rate-limit authentication endpoints to around 5–10 requests per minute. APIs should also default to "deny" access and return generic error messages to avoid exposing internal system details.
API Monitoring and Rate Limiting
After establishing strong authentication practices, the next step in protecting your API is to implement monitoring and rate limiting. These measures ensure your API remains responsive and secure, even under heavy use. While authentication protects access, rate limiting prevents clients from overwhelming your system. Monitoring, on the other hand, helps you spot unusual activity and address potential threats before they escalate. Together, they create a robust safety net for your API.
Rate Limiting and Throttling Techniques
Rate limiting works by controlling how many requests a client can make within a set timeframe. Different algorithms are used to enforce this, depending on the needs of your system. For example:
- The token bucket algorithm allows controlled bursts of traffic, making it ideal for APIs that experience occasional spikes.
- The sliding window counter provides accurate and efficient request management, making it suitable for most production environments.
"Rate limiting is less about saying 'no' and more about ensuring your API can consistently say 'yes' to legitimate requests without crumbling under pressure." - getlate.dev
For distributed systems, tools like Redis can synchronize counters across multiple servers, maintaining consistency. It's also essential to provide clear feedback to API users. Include headers like X-RateLimit-Limit, X-RateLimit-Remaining, and X-RateLimit-Reset in responses. These headers help developers track their usage and avoid exceeding their quota. If a client does hit their limit, respond with an HTTP 429 Too Many Requests status and include a Retry-After header to guide them on when they can try again.
For APIs with resource-heavy endpoints, consider a points-based system. Assign higher "costs" to actions like batch exports or complex searches, ensuring these operations don't overload your infrastructure. For example, the GitHub API allows 5,000 requests per hour for authenticated users, while unauthenticated users are limited to just 60 requests per hour. Similarly, OpenAI GPT-4 (Tier 1) enforces limits of 500 requests and 10,000 tokens per minute. These tiered approaches balance user access with system stability.
Once rate limiting is in place, the focus shifts to monitoring for real-time insights.
Real-Time Monitoring Tools
Monitoring tools are critical for analyzing traffic patterns and detecting anomalies. They help establish usage baselines - like peak traffic times and average requests per user - while also identifying long-term trends. Automated systems can flag unusual activity, such as sudden traffic spikes from a single IP, excessive failed login attempts, or unexpected traffic during off-hours. In 2025, 41% of API security incidents involved resource abuse like brute force attacks and data scraping, highlighting the importance of real-time detection.
Some key metrics to monitor include:
- Request frequency: Tracks how often users interact with your API.
- Payload sizes: Flags unusually large requests that could indicate abuse.
- Error rates: A high number of 429 errors (rate limit hits) can signal overly strict limits or malicious activity.
If the rate limit hit rate exceeds 5%, it may be time to adjust your thresholds or investigate potential abuse. Modern tools can dynamically adapt limits based on server load, reducing quotas when CPU usage exceeds 80% or error rates surpass 5%. This approach saved a Fortune 500 company from a major outage when a misconfigured script made 47 million requests to Stripe's API over six hours. Stripe's rate-limiting system automatically throttled the offending client.
Finally, set up dashboards to send instant alerts - via Slack, email, or other channels - when usage nears 75–90% of a quota or when 429 errors spike. API gateways like Kong, AWS API Gateway, and Nginx act as a first line of defense, blocking malicious traffic before it reaches your servers. For login routes, progressive delays (e.g., adding a one-second delay after three failures) can deter brute-force attacks while still accommodating legitimate users who mistype their credentials.
Data Protection and Encryption
Data protection is all about keeping information safe during both transmission and storage. The main idea? Make sure sensitive data doesn't fall into the wrong hands - whether it's intercepted while being sent or accessed from compromised storage. Techniques like encryption and input validation are key to stopping threats like injection and man-in-the-middle attacks.
Input Validation and Sanitization
Input validation acts as your system's first shield against harmful data. The concept is straightforward: every piece of incoming data gets checked before it interacts with your core processes. This step is crucial to block attackers from injecting malicious code or overloading your API with malformed requests. Using allowlisting - defining what is explicitly acceptable - is far more secure than denylisting, which crafty attackers can often bypass.
"Input validation should happen as early as possible in the data flow, preferably as soon as the data is received from the external party." - OWASP
Tools like JSON Schema, Pydantic (for Python), or Zod (for TypeScript) make schema validation easier. These tools automatically reject requests that don’t meet your structure, catching errors like incorrect data types, missing fields, or invalid values. When dealing with databases, always use parameterized queries or ORMs to ensure user input is treated as data, not executable code, reducing the risk of SQL injection.
Set strict limits on input length and size to avoid buffer overflows and denial-of-service attacks. For instance, if usernames are capped at 50 characters, reject anything longer. Similarly, for file uploads, enforce size restrictions and validate file types. When displaying user data in API responses, use output encoding libraries like DOMPurify to sanitize content and neutralize Cross-Site Scripting (XSS) risks by encoding potentially harmful characters.
With these measures in place, you can prevent many injection and overflow vulnerabilities. The next step is securing your data through encryption.
Encryption Standards and Protocols
Encryption plays a critical role in protecting sensitive data, complementing other security measures like strong authentication and rate limiting. For data in transit, TLS 1.3 is the gold standard. It's faster and more secure than TLS 1.2, requiring fewer handshake steps and eliminating outdated ciphers. While TLS 1.2 should remain the minimum for compatibility, aim to adopt TLS 1.3 wherever possible. Adding an HTTP Strict Transport Security (HSTS) header ensures all communication is forced over HTTPS. For example:
Strict-Transport-Security: max-age=31536000; includeSubDomains; preload
This setup helps block protocol downgrade attacks by ensuring browsers only connect through encrypted channels.
For mobile applications requiring high security, use certificate pinning to prevent man-in-the-middle attacks involving fake certificates. In server-to-server communication, HMAC signing ensures data integrity and authenticity. Automate certificate management with tools like Let's Encrypt or AWS Certificate Manager to avoid disruptions caused by expired certificates.
When it comes to data at rest, encrypt sensitive fields in your database using AES-256 or stronger algorithms. Passwords should never be stored in plaintext; instead, hash them with modern algorithms like Argon2 or bcrypt, using at least 10 salt rounds for added security. For signing JWTs, asymmetric algorithms like RS256 or ES256 are preferred, as they allow secure validation without sharing private keys. Regularly rotate cryptographic keys with a Key Management Service (KMS) or Hardware Security Module (HSM) to maintain security over time.
| Security Layer | Recommended Standard | Purpose |
|---|---|---|
| Data in Transit | TLS 1.3 / mTLS | Encrypt communication and verify identities |
| Data at Rest | AES-256 | Protect sensitive stored information |
| Passwords | Argon2 / bcrypt | Prevent credential theft with secure hashing |
| Token Signing | RS256 / ES256 | Enable scalable, secure JWT validation |
"Gartner predicts that by 2026, APIs will be the most frequent attack vector for enterprise web applications, surpassing traditional web interfaces." - Gartner
As quantum computing evolves, it’s essential to prepare for crypto-agility - the ability to quickly update encryption algorithms when current ones become outdated. Staying ahead by enforcing TLS 1.3 and keeping cipher suites current will position your API to adapt to future quantum-safe cryptography.
Security Testing and Governance
Security testing and governance are essential to identifying vulnerabilities and maintaining control over APIs. With 95% of organizations reporting an API security incident in the last 12 months, having systematic testing processes and clear governance frameworks is no longer optional - it’s a necessity.
Security Testing Methods
Effective API security testing involves multiple approaches that work together. Static Application Security Testing (SAST) examines your source code without executing it, helping to catch issues like hardcoded credentials or weak cryptographic implementations early in the development process. On the other hand, Dynamic Application Security Testing (DAST) evaluates the API while it’s running, sending live requests to detect vulnerabilities such as injection flaws or authentication bypasses.
Traditional scanners often fall short when it comes to API-specific risks. As AquilaX puts it:
"API security is qualitatively different from web security. Traditional web scanners understand HTML forms and cookies. They don't understand REST semantics, JWT token structures, multi-tenant data models, or GraphQL introspection."
This highlights the need for specialized API testing tools.
One of the most critical vulnerabilities to address is Broken Object Level Authorization (BOLA), ranked as the top risk in the OWASP API Security Top 10. Unfortunately, most automated scanners fail to detect BOLA. To test for it, you must verify that the API enforces proper ownership checks before granting resource access.
Design-time specification auditing is another proactive measure. Tools like 42Crunch can audit OpenAPI specifications against more than 300 security checks, flagging issues such as missing authentication or overly permissive schemas during the design phase. By integrating these audits into your CI/CD pipeline, you can block code merges if security scores fall below acceptable thresholds. For runtime testing, use tools like OWASP ZAP or StackHawk to run automated DAST scans on staging environments for every pull request.
Fuzz testing is also valuable - it involves sending random or malformed data to endpoints to uncover crashes or memory leaks. Additionally, systematically test rate limits by bombarding endpoints with 1,000+ requests per second and checking for pagination abuse using extreme parameters like ?page_size=999999.
After testing, strong governance practices ensure that APIs remain secure over time.
API Governance Practices
While authentication, monitoring, and data protection secure API traffic, governance provides the oversight needed to maintain security consistently. Undocumented endpoints (often called "shadow APIs") and deprecated endpoints still in use ("zombie APIs") pose significant risks. Discovery tools can analyze traffic from API gateways and cloud environments to compare active endpoints against documented specifications, helping to identify these gaps.
Centralized policy management through API gateways is crucial for enforcing uniform authentication, authorization, and rate-limiting rules across all endpoints. This consistency is vital, especially when API attacks have surged 400% year-over-year and the average cost of an API-related breach now stands at $4.5 million. To minimize risks, follow Semantic Versioning (SemVer) standards and provide clear deprecation notices with specific sunset dates, encouraging clients to migrate away from outdated and vulnerable versions.
Regular audits are also key. They ensure APIs comply with internal policies and regulations like GDPR, HIPAA, and PCI DSS v4.0 (specifically Requirements 6.2 and 6.3). Audit logs should record authentication failures and unusual data access patterns while excluding sensitive data. Assigning correlation IDs to every request can simplify transaction tracing across microservices, making security investigations and debugging more efficient.
Finally, secure storage and management of API keys and tokens are critical. Use tools like HashiCorp Vault or AWS KMS to store credentials securely and rotate them on a defined schedule. This step is particularly important given that GitHub's secret scanning program identified over 1 million exposed secrets in public repositories in 2023, with API keys being a major category. Automated secret management can help keep your credentials safe and out of those statistics.
Low Code and No Code Platforms for API Security
Securing APIs often involves intricate custom development, but low-code and no-code platforms simplify the process by embedding security features right into their frameworks. This reduces coding requirements while maintaining strong defenses.
Benefits of Low Code/No Code for API Security
These platforms make implementing security much easier through visual tools. Features like MFA, SSO, and RBAC can be configured using drag-and-drop interfaces. Advanced protections, including JWT validation, OAuth 2.0, and mTLS, are often deployed as edge policies to block threats before they even reach your server. As Zuplo highlights:
"Security policies run at the edge, blocking malicious requests before they reach your origin server."
Additionally, these platforms ensure consistent data protection by integrating TLS and AES-256 encryption for both data at rest and in transit. They also validate requests against OpenAPI schemas, rejecting malformed or unauthorized data. Built-in support for secrets management tools like AWS Secrets Manager or HashiCorp Vault eliminates the need for custom integrations.
Another key advantage is centralized governance. API gateways provide a unified control plane for managing versioning, routing, and security across all APIs, whether hand-coded or low-code. This helps prevent "API sprawl" and ensures comprehensive protection. Gartner underscores the growing relevance of these platforms:
"By 2025, 70% of new applications developed by enterprises will use low-code or no-code technologies."
With 87% of enterprise developers now using these platforms in some capacity, and the no-code market expected to grow from $28.11 billion in 2024 to $93.92 billion by 2029, their role in secure API development is only expanding.
When choosing a platform, look for features like built-in rate limiting, Web Application Firewalls (WAFs), and integrations with real-time monitoring tools like Datadog, New Relic, or Splunk. Set up RBAC during onboarding to ensure users can only access what they need for their roles. Many platforms also include compliance tools for regulations like GDPR, HIPAA, and SOC 2, simplifying audits.
Finding Platforms with the Best Low Code & No Code Platforms Directory
Choosing the right platform is essential for seamlessly integrating security into your API strategy. The Best Low Code & No Code Platforms Directory (https://lowcodenocode.org) is a valuable resource for finding platforms that support advanced security features like mTLS, JWT validation, and edge-native WAFs. The directory compares tools across categories such as development, automation, and web app building, helping you find the perfect fit for your needs.
For example, platforms like Knack focus on database-centric security, offering granular role-based permissions and data isolation - ideal for SMBs or teams with many users. Quickbase caters to regulated industries with SOC 2/HIPAA compliance and workflow automation, starting at around $8,500 per year for 10 users. On the other hand, Zuplo provides a free tier, allowing developers to secure APIs without upfront costs.
The directory also allows developers to submit their tools for exposure, connecting creators with potential users. Use it to filter platforms based on specific security needs, such as centralized API management, automated compliance reporting, or seamless integration with your secrets management tools. This helps you save time and ensures your platform aligns with your security priorities - without the need for extensive custom coding.
Conclusion
Securing APIs must start with the very first endpoint. With API attacks expected to increase by an astonishing 996% by 2030 and the average breach costing $6.1 million, organizations cannot afford to overlook this critical aspect of their infrastructure. The December 2024 U.S. Treasury breach serves as a cautionary tale: Chinese state-backed hackers exploited a compromised API key from BeyondTrust, gaining access to government workstations. This incident highlights the vulnerabilities even advanced organizations face when security measures fall short, emphasizing the importance of a layered defense strategy.
A strong, multi-layered security approach is non-negotiable. Key measures include implementing robust authentication protocols like OAuth 2.0 and OpenID Connect and enforcing strict authorization checks to address vulnerabilities such as BOLA. Rate limiting across users, IPs, and endpoints can thwart brute-force attempts, while enforcing TLS 1.2+ ensures secure traffic. Additionally, validating inputs against schemas adds another layer of protection.
"API security is not a feature you add at the end of development - it is a design principle that must be present from the first endpoint." – ECOSIRE Research and Development Team
Visibility is just as critical as protection. Alarmingly, only 27% of organizations maintain a comprehensive and up-to-date API inventory, leaving shadow APIs as significant risks. Continuous discovery tools and centralized API gateways can close these gaps by standardizing security policies across an organization’s infrastructure. Real-time monitoring further enhances protection by identifying unusual patterns - like spikes in 4xx/5xx errors or unexpected geographic traffic - before they evolve into major breaches.
Modern platforms make secure API development more accessible. Low-code and no-code platforms embed security features into user-friendly visual frameworks, simplifying the process. For those seeking resources, the Low Code & No Code Platforms Directory (https://lowcodenocode.org) provides a curated list of tools designed to integrate strong API security practices. Leveraging such platforms allows organizations to automate processes and adopt best practices with ease. Proactive prevention is always more cost-effective than dealing with the aftermath of a breach.
FAQs
How can I prevent BOLA in my API?
To safeguard your API from Broken Object-Level Authorization (BOLA) vulnerabilities, it's crucial to implement strict authorization checks for every object or resource access. This means verifying that users are explicitly allowed to access the specific object IDs included in each request.
Beyond manual checks, leveraging automated security testing can help uncover vulnerabilities more efficiently. Additionally, integrating AI-driven tools to monitor API behavior can provide an extra layer of protection, enabling you to detect and address potential BOLA issues before they make it to production.
What rate limits should I start with?
A sensible starting point for rate limiting is about 1,000 requests per hour per user or API key. From there, you can fine-tune the limit based on your traffic patterns and how your system is being used. This helps maintain a balance between performance and security.
Which data should be encrypted vs hashed?
Sensitive data, such as personal details, login credentials, and financial information, should always be encrypted to keep it confidential. Passwords and other authentication credentials are commonly hashed, adding an extra layer of protection. Even if this data is compromised, hashing ensures it remains secure, aligning with established security practices.

