Low-code platforms have made app development accessible to non-technical users, but they also bring challenges like security risks, compliance issues, and managing app sprawl. To address these, organizations are adopting a three-layer governance framework:
- Policy: Defines rules for data access and classification.
- Platform: Provides pre-approved tools, connectors, and service catalogs.
- Process: Automates monitoring and approvals using policy-as-code.
Without governance, companies face risks like unmanaged apps, rising costs, and security vulnerabilities. For example, introducing mandatory app expiration policies helped one company reduce active apps by 50% and save $120,000 annually. Tools like Open Policy Agent (OPA), service meshes, and observability platforms help enforce governance while maintaining development speed.
Key strategies include:
- Using policy-as-code to automate compliance checks.
- Implementing service meshes for centralized control over distributed microservices.
- Leveraging observability tools for real-time monitoring.
- Offering pre-approved templates to simplify secure app development.
ServiceNow Low-Code Governance: App Engine Management Center
sbb-itb-3a330bb
Governance Challenges in Low Code Microservices
When citizen developers dive into low-code platforms, they often encounter three main hurdles: security weaknesses, compliance oversights, and uncontrolled scaling. These challenges can escalate quickly, as non-technical users may not fully grasp enterprise-level security protocols or regulatory demands.
Security Vulnerabilities in Low Code Microservices
Low-code platforms often rely on client-side data filters by default, which can inadvertently allow users to bypass interface restrictions and access sensitive data. On top of that, microservices built on these platforms remain exposed to traditional threats like SQL injections, HTML injections, and OS command exploits - especially when user inputs aren't properly sanitized.
Third-party API connectors introduce another layer of risk. Many of these connectors use shared credentials or excessive OAuth permissions, creating a potential single point of failure. To address this, organizations can deploy tools like HashiCorp Vault to manage secrets. These tools issue short-lived, temporary credentials instead of embedding static keys directly into connectors, reducing the attack surface significantly.
Meeting Compliance and Regulatory Standards
Compliance is another major sticking point for low-code microservices. As micro-apps multiply, maintaining oversight of regulated data becomes harder. For instance, the launch of the AWS European Sovereign Cloud in January 2026 brought in strict data residency rules, requiring companies to enforce geo-fencing policies to ensure sensitive data stays within approved regions.
Research from early 2026 highlights that fragmented data controls and weak governance frameworks are the primary obstacles to scaling enterprise AI and automation. However, automated governance frameworks have shown promise, cutting security incidents tied to micro-apps by 70% within six months. One effective approach is implementing policy-as-code with tools like Open Policy Agent (OPA). By embedding compliance rules directly into the CI/CD pipeline, these tools can automatically block non-compliant deployments before they even go live.
Managing Scalability and Service Dependencies
Beyond security and compliance, scaling microservices and managing their dependencies present additional governance challenges. inefficient micro-apps can overload APIs, highlighting why API gateway integration is critical for managing traffic, leading to skyrocketing cloud costs and unpredictable infrastructure expenses. The "noisy neighbor" problem is a common issue in distributed environments, where one micro-app consumes disproportionate resources, negatively impacting the performance of other services.
As micro-apps proliferate, organizations often face "tool sprawl" - a tangled mess of unmanaged third-party connectors and fragmented APIs. This complexity makes it harder to track dependencies and increases the likelihood of system-wide failures when external APIs are updated or deprecated. Implementing a centralized catalog for micro-apps can help mitigate this problem. Companies that have adopted this approach report a 45% drop in duplicate applications, streamlining their operations significantly.
"Speed without guardrails becomes technical debt at scale." - Smartstorage.Host
Unchecked growth in low-code environments may seem like rapid progress, but without proper governance, it can spiral into costly inefficiencies and vulnerabilities.
Tools and Practices for Microservices Governance
Managing governance in low-code microservices environments means finding ways to enforce rules without slowing down development. By using tools like policy engines, service meshes, and observability platforms, governance can shift from being a roadblock to an automated safety net that works quietly in the background.
To address concerns such as security vulnerabilities and compliance gaps, several low-code tools and practices have become essential.
Policy Management and Central Repositories
Open Policy Agent (OPA) has become a go-to solution for enforcing policies as code using its Rego language. It automatically checks compliance during service creation ("On Save") and during pipeline execution ("On Run"). This ensures that policies can be versioned, tested, and applied just like application code, reinforcing the "Policy" layer within the governance framework.
Central repositories play a critical role by acting as the single source of truth for all microservices. Tools like Backstage or git-backed YAML repositories help track details such as ownership, data classification, and compliance status for every micro-app. For example, during a 30-day pilot at a company with 5,000 employees, implementing a governed registry and automated templates led to 75% of 120 micro-apps being auto-approved - all while maintaining zero security incidents.
Real-time enforcement is handled by API gateways and middleware, which apply measures like data masking, rate limiting, and quota management before backend services are accessed. To further secure the ecosystem, enterprise secrets stores integrate with policy checks, eliminating plaintext credentials. Additionally, tools like Snyk, Dependabot, and Semgrep run automated scans within CI pipelines to enforce security checks, such as Software Composition Analysis (SCA) and Static Analysis (SAST), before deployment.
Dynamic enforcement, however, requires more than static policies. This is where distributed control mechanisms, like service meshes, come into play.
Service Meshes for Distributed Governance
While repositories handle static enforcement, dynamic control is achieved through service meshes. A service mesh centralizes governance for distributed microservices without requiring changes to the application code. For example, Red Hat OpenShift Service Mesh 2.4, built on Istio and Envoy Proxy, provides key features like mutual TLS (mTLS) and service-to-service authentication to support zero-trust security.
"Red Hat OpenShift Service Mesh addresses a variety of problems in a microservice architecture by creating a centralized point of control in an application. It adds a transparent layer on existing distributed applications without requiring any changes to the application code." – Red Hat Documentation
This mesh layer separates governance policies from the application layer, enabling platform engineers to adjust access controls or rate limits globally without involving developers. This approach strengthens the "Platform" layer of the governance framework. It also helps enforce API quotas, preventing issues like "noisy neighbor" scenarios and runaway cloud costs caused by inefficient low-code scripts. Additionally, service meshes provide consistent telemetry across all services, offering detailed insights into dependencies, traffic patterns, and performance metrics.
The next step in governance involves using observability tools to monitor and analyze these distributed systems in real time.
Observability and Monitoring Solutions
Observability tools are essential for tracking compliance, debugging, and ensuring the health of microservices across distributed environments. The ELK Stack (ElasticSearch, LogStash, Kibana) is a popular choice for monitoring, alerting, and event tracking, while Nagios keeps an eye on storage, CPU, memory, and network usage, triggering alerts when thresholds are breached.
Tools like Spring Actuator and JMX enable health monitoring by collecting service statistics through "push" and "pull" mechanisms. Meanwhile, service registries such as Kubernetes ensure that continuously deployed microservices remain discoverable and operational. Audit logging adds another layer of compliance, complementing the earlier discussed governance measures.
| Tool Category | Specific Solution | Primary Governance Function |
|---|---|---|
| Policy Engine | Open Policy Agent (OPA), Harness Policy as Code | Centralized rule definition and enforcement |
| App Catalog | Backstage, git-backed YAML | Canonical inventory and lifecycle tracking |
| Secrets Store | HashiCorp Vault, AWS Secrets Manager | Secure credential management and rotation |
| CI/CD Gating | GitHub Actions, GitLab CI, OPA Gatekeeper | Automated security and policy scans |
| Observability | ELK Stack, Nagios, Spring Actuator/JMX, Kubernetes | Monitoring service events, health, and compliance metrics |
Platform-Specific Governance Strategies
While many governance tools and practices apply broadly across low-code development platforms, Mendix, ServiceNow, and Salesforce each bring their own governance frameworks tailored to their specific architectures and philosophies.
Mendix's Reusable Components Framework
Mendix takes a structured approach to governance with its Private Marketplace model, giving administrators complete oversight of the components developers can access. This marketplace ensures all modules, widgets, and connectors are vulnerability-scanned through Quality Solutions Management (QSM) before being made available.
"The Private Marketplace lets companies privately share company content with other platform users. It is controlled and curated by administrators, which means the content adheres to specific company guidelines." – Mendix
To maintain consistency across microservices, organizations can deploy starter apps preloaded with branding, security configurations, and standard modules. The Atlas UI framework adds another layer of uniformity by offering UI resource packages that combine templates and styling, ensuring a cohesive design language across applications.
Mendix also reduces logic duplication by encouraging teams to expose microflow logic through REST APIs or OData, creating a centralized source of truth. To maintain clarity and efficiency, Mendix recommends keeping individual apps below 3,000 microflows and 750 entities, while limiting microflows to no more than 25 elements.
This modular and reusable approach stands in contrast to platforms like ServiceNow and Salesforce, which integrate governance more deeply into their centralized data and workflow systems.
ServiceNow and Salesforce Shared Services Model
Unlike Mendix, which focuses on component-level reusability, ServiceNow and Salesforce emphasize centralized governance through unified platforms.
Both platforms rely on centralized data and workflow engines to manage governance. Salesforce uses Data Cloud (Data 360) to unify data across CRM, IT, and HR systems, while ServiceNow digitizes enterprise workflows through its single cloud-based platform. A key feature of both systems is their use of dynamic Configuration Management Databases (CMDB), which track real-time dependencies and assets - an essential tool for managing microservices and shared integrations.
In 2024, Crestron Electronics selected Salesforce over ServiceNow to unify their global technical support operations. Matthew Paupst, VP of Global Technical Support, highlighted the benefits:
"We chose Salesforce vs. ServiceNow and the other contenders because of the experience we were going to be able to provide with Service Cloud. And the data that we were going to be able to take action on."
This implementation centralized Crestron’s data across global operations while leveraging Salesforce's built-in approval workflows and integration controls to maintain governance.
Both ServiceNow and Salesforce also support reusable module frameworks with embedded policy enforcement tools. Administrators can define rules for API access and establish approval workflows for new application deployments, reinforcing security and compliance. Additionally, Salesforce’s Agentforce allows AI agents to operate within strict security guidelines, with clear escalation paths to human representatives. For industries with stringent compliance needs, Salesforce offers specialized solutions - such as its Public Sector and Financial Services clouds - that automate adherence to regulatory standards like FFIEC, HITRUST, and PSD2.
These centralized governance strategies enable ServiceNow and Salesforce to maintain control over microservices while ensuring compliance and security in low-code environments.
Comparing Governance Approaches
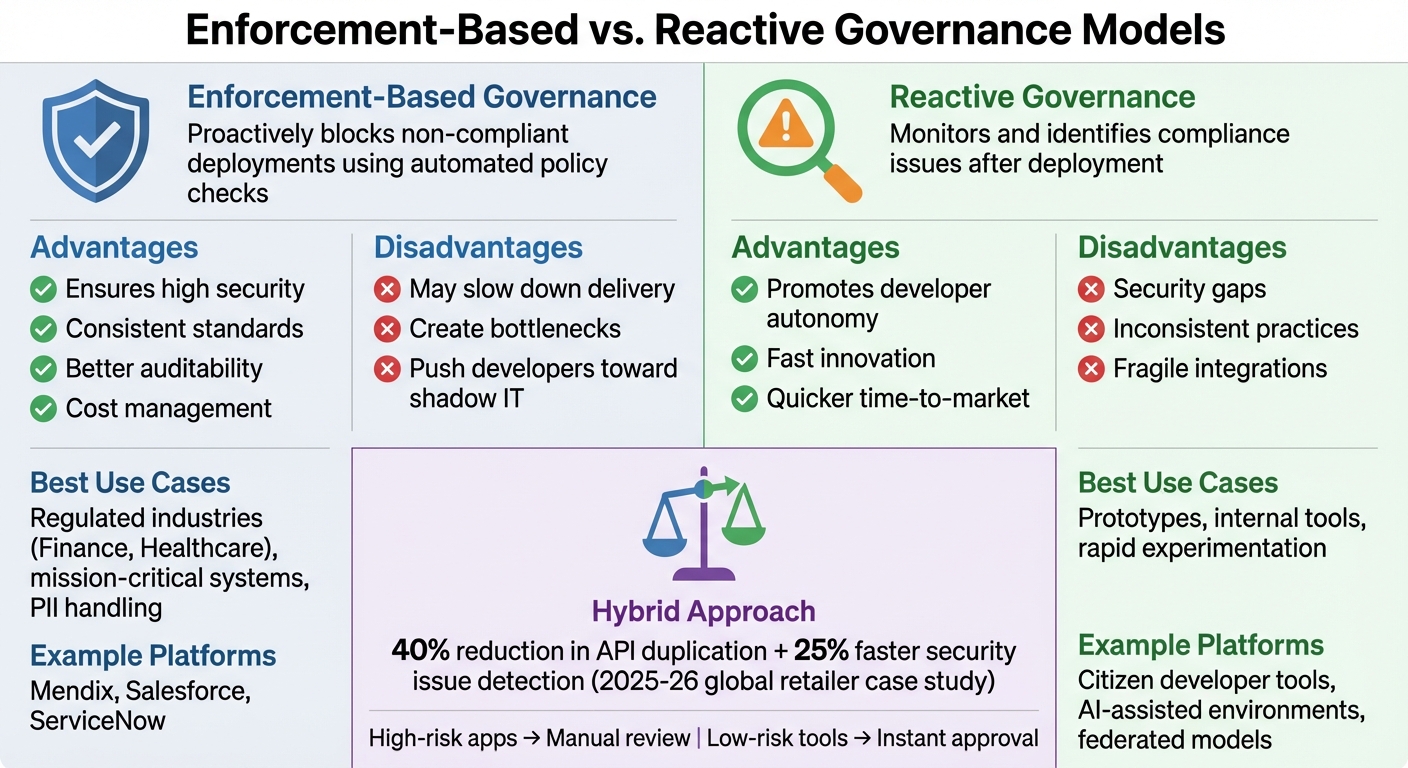
Enforcement-Based vs Reactive Governance Models for Low-Code Microservices
When organizations use low-code platforms to build microservices, they face a critical decision: should they focus on prevention or rely on post-deployment detection? This choice directly affects development speed, security, and compliance, adding another layer to the challenges of managing risks like scalability and regulatory adherence in low-code environments.
Enforcement-based governance focuses on stopping non-compliant deployments before they go live. Using tools like policy-as-code, platform teams can automatically reject apps that fail to meet security standards, data residency rules, or architectural guidelines. This method works especially well in industries like finance and healthcare, where even minor compliance violations can lead to heavy penalties. However, the trade-off is a potential slowdown in development, especially if approval processes aren’t fully automated, which can frustrate citizen developers and create bottlenecks.
On the other hand, reactive governance allows teams to deploy first and monitor afterward. By leveraging observability tools and service registries, issues can be identified and addressed in production. This approach prioritizes developer freedom and speeds up innovation, making it ideal for low-risk projects like internal prototypes. But it comes with risks: shadow IT, security vulnerabilities, and fragmented integrations can escalate if not carefully managed.
By early 2026, many organizations have embraced hybrid governance models. These models combine strict enforcement for high-stakes systems with reactive monitoring for experimental projects, aligning governance strategies with varying operational risks. For example, a global retailer implementing this approach in 2025–26 reported a 40% reduction in API duplication and a 25% faster detection of security issues. Their success came from automating risk classification during app onboarding. High-risk apps handling sensitive data triggered manual reviews, while low-risk tools were approved instantly. This tiered strategy supports the three-layer governance framework (Policy, Platform, Process) by applying different levels of oversight based on risk profiles.
Enforcement-Based vs. Reactive Governance Models
| Feature | Enforcement-Based Governance | Reactive Governance |
|---|---|---|
| Description | Proactively blocks non-compliant deployments using automated policy checks | Monitors and identifies compliance issues after deployment |
| Advantages | Ensures high security, consistent standards, better auditability, and cost management | Promotes developer autonomy, fast innovation, and quicker time-to-market |
| Disadvantages | May slow down delivery, create bottlenecks, and push developers toward shadow IT | Risks include security gaps, inconsistent practices, and fragile integrations |
| Best Use Cases | Regulated industries (e.g., Finance, Healthcare), mission-critical systems, PII handling | Prototypes, internal tools, and rapid experimentation |
| Example Platforms | Mendix (strict guardrails), Salesforce (Shared Services Model), ServiceNow | awesome nocode and lowcode tools, AI-assisted environments, federated models |
As AI continues to shape compliance automation, these governance models are evolving. According to Codeguru.App, "AI will take the path of least resistance - make sure your platform is that path for secure, compliant micro apps". Organizations offering pre-approved templates are finding that developers naturally adhere to compliance standards without feeling constrained, paving the way for smoother, more secure development processes.
Best Practices for Implementing Microservices Governance
You don’t need to overhaul your entire system to implement effective governance for low-code microservices. Start with a quick 30-day containment phase focused on three key actions: require enterprise Single Sign-On (SSO), apply mandatory data classification labels, and enable basic cost tagging. These steps address common security gaps while keeping development on track. This initial phase lays the groundwork for more long-term governance strategies.
To make governance sustainable, compliance should be the easiest option. Pre-approved security templates - like those mentioned in the tools section - can make this possible. By offering citizen developers templates that include security features such as TLS 1.3 and OIDC authentication, you simplify deployment while minimizing the risk of shadow IT workarounds.
Automation plays a big role in reducing the workload for developers and governance teams alike. Automated governance frameworks, for example, have cut security incidents tied to micro-apps by 70% within six months. Tools like policy-as-code with OPA can block deployments connecting to unapproved external domains, cutting down on manual reviews. This allows security teams to focus on higher-risk applications instead of routine checks.
That said, automation can’t replace human oversight. Pairing citizen developers with experienced engineers through a "buddy" review system ensures better adherence to governance standards early on. Additionally, short, focused training sessions (1–2 hours) on topics like data handling, secrets management, and AI safety can help developers avoid common pitfalls. For shadow IT already in use, create an "amnesty" onboarding process. Use SSO and SIEM logs to identify unmanaged apps and offer a simple registration process to bring them into compliance.
Governance should be treated as a dynamic system that evolves with your organization’s needs. For example, assign expiration dates to micro-apps and use automated workflows to disable or archive apps after 30 days of inactivity. Replace long-lived API keys with ephemeral credentials managed through a centralized secrets manager, issuing short-lived tokens at runtime for added security. These measures not only improve security but can also reduce unplanned cloud spending by 30%–70% while speeding up delivery timelines.
Conclusion and Additional Resources
In today’s landscape, where security, compliance, and scalability challenges are ever-present, governance has become indispensable. Microservices governance provides the structure needed for non-developers to safely deploy at scale. Hybrid governance - combining centralized policies with decentralized execution - strikes a balance between maintaining speed and ensuring security. With 87% of enterprise developers now incorporating low-code platforms into their workflows and the market expected to reach $44.5 billion by 2026, governance is no longer optional - it's a necessity.
A robust governance framework connects People, Process, and Technology to address critical areas like identity management, data residency, CI/CD, and cost control. Start by implementing rapid containment measures, then advance toward comprehensive policy-as-code enforcement.
"Citizen development is not the enemy - it's inevitable. The goal of governance is to keep speed while reducing risk." – Florence.Cloud
For those ready to act on these strategies, the Best Low Code & No Code Platforms Directory serves as a valuable resource. This directory allows you to compare platforms based on features like Policy-as-Code integration, Attribute-Based Access Control (ABAC), and automated lifecycle management. It also highlights platforms offering centralized control centers, private marketplaces for pre-vetted components, and support for sovereign cloud regions - key to meeting 2026 data residency requirements.
Whether you're overseeing hundreds of marketing micro-apps or developing regulated financial tools, the right platform can turn governance into a competitive advantage. Explore platforms with features like streamlined CI/CD pipelines, automated SBOM generation, and centralized secrets management to transform governance from a roadblock into an enabler.
FAQs
What’s the fastest way to start governing low-code microservices?
The fastest way to manage low-code microservices effectively is to set up a governance framework with essential controls like policies, approval workflows, and lifecycle management. Begin by focusing on app approval processes, data access policies, and integration rules to minimize potential risks. Incorporate identity-first access controls, using role-based permissions and automated templates for onboarding and CI/CD pipelines. This approach ensures security and compliance without sacrificing efficiency.
How do I enforce data residency and compliance automatically?
To simplify data residency and compliance, leverage governance frameworks that incorporate policy-as-code, automated templates, and real-time controls. A few essential practices include:
- Using predefined policies for role-based access control (RBAC), data classification, and residency during onboarding.
- Implementing identity-first access controls and role-based entitlements to ensure secure and compliant access.
- Employing tools like CI/CD pipelines and gated export controls to keep data handling aligned with regulatory requirements.
- Establishing residency gates to block deployments outside approved regions.
These measures make it easier to maintain compliance, even in low-code environments, by automating key aspects of governance.
When should we use enforcement-based vs. reactive governance?
Enforcement-based governance is ideal for environments where compliance is non-negotiable, such as those dealing with sensitive data or operating under strict regulations. This approach uses mandatory policies and rigid access controls to minimize risks like data breaches or violations of regulatory standards.
On the other hand, reactive governance shines in dynamic, less-regulated settings. It emphasizes real-time monitoring and policy adjustments, offering the flexibility needed when business users or citizen developers rapidly create micro apps. This adaptability ensures policies keep pace with the ever-changing demands of fast-moving environments.


